How Safe Is Google Drive? How Can You Improve this Security?
 Image Source: NordVPN
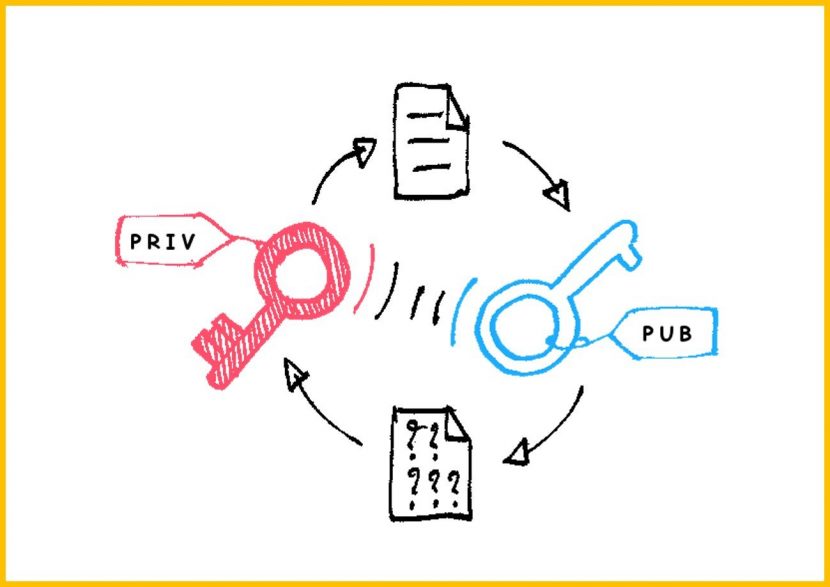
Image Source: NordVPN
In this article we are going to answer one of your most concerning question: How secure is Google Drive?
Google Drive is one of the top free online cloud-based data storage and sharing solutions available to Google users. Its importance was increased tremendously especially after the spread of COVID-19 and the subsequent lockdowns when users were forced to resort to online platforms for transferring large amounts of data that they could otherwise do offline. Transferring or even backing up heavy files is not as easy as it sounds, as many services or applications tend to lower the quality of the data (For example compressing pictures and lowering resolution), which Google Drive does not do, making it a strong contender for the job.
Being able to access files from any device and anywhere in the world also makes Google Drive a user-favorite service. Since Google Drive also offers online collaborative editing in Office Suit e.g. Google Docs, Google Sheets, and Google Slides, students are increasingly becoming inclined to shift to Google Drive for academic projects. Storing data online, however, also raises privacy concerns in many of us and so, the question of “How secure is Google Drive?” comes up. In this day and age, it is very important to be able to answer this question. Therefore, if you want to find out the answer, keep reading!
Google is a trillion-dollar Internet giant that recognizes the importance of data security and user privacy. However, with a history of profiting from user data, we still ponder over the question of how secure is Google Drive?
Before getting into the science of how Google stores its data and all the protocols that come along, it is important for us to remember that the easiest way for a hacker to breach your security is through malware or tricking you into telling them your password. Safe internet practices must never be neglected to ensure privacy and data security.
To be able to understand the question of how secure is Google Drive, it is important we discuss Google’s security policy as an entire service.
Contents
Google’s Security Policy:
Google, a global enterprise, is fully aware of the need to have a user security-first approach. For this, Google is compliant with ISO, SOC, PCI, GDPR, HIPPA, and the EU Model Contract Clause. You can read Google’s Security Policy here and even access the Transparency Logs to understand better the rules and regulations Google is inclined to follow when dealing with your personal data.
How Data is Secured Online
Since this article aims to inform you in a simpler way how securing online data works, it would help to revisit what security entails and what processes are followed to make this security possible.

What is Encryption?
It is important to understand some terms that are associated with the entire online-security process. The term encryption, perhaps, leading the list, means taking data that is understandable by users (called plaintext) and converting it into data that is output (ciphertext) in a format that does not reveal legible information about the plaintext. The algorithm that does this is available on public platforms. However, the decryption of this ciphertext cannot be done without a secret key. Google Drive employs the same method to secure its user data. It is, therefore, safe to say that Google Drive provides its users with the ultimate security program. Now, the question arises: How secure is Google Drive?
How Secure is Google Drive and how does it Secures Users’ Data
Google Drive uses a 128 bit Advances Encryption Standard (AES) key to store your data while it is stored in the drive and 256 bit SSL/TLS encryption when the data is moving from one point to another. In transit, the data is most vulnerable and in danger of being hacked by snooping hackers so that is why Google Drive uses a robust 256 bit SSL/TSL encryption. That makes data pretty secure but not 100% safe. The greater the encryption is, the harder it would be for anyone to decrypt what they have collected.
Google Drive employs multiple layered security for enhanced data protection; apart from encryption, it also separates the data into different packets, rendering the individual packets useless to anyone. Every data packet has its own encryption key. The content stored by Google is divided up into smaller packets with designated security keys that are encrypted with further keys. The latter key gives an added layer of security and is managed by Google’s key management service (KMS-Key Administration Management). Now, let’s address the question: How secure is Google Drive?
When you update a file or document, a new key is generated for that packet of data and the old one is discarded thus boosting overall security. In this case, if the data is hacked, the data will not be readable without the encryption keys. This kind of encryption for stored data is known as “Encryption at Rest”.
Now, before moving forward, let us understand a little more about “Encryption at Rest”.
a. Encryption at Rest:
All data on Google Drive is automatically encrypted for safe storage (“at rest”, in contrast to “in transit”). A common cryptographic library, called Tink, is used by Google for this purpose and it ensures that updated files have new security keys and the old ones are discarded.
Another loophole hackers can benefit from is through looking for data that is being transferred without a secure method. Sometimes, when data is being shared with other users (who may even have restricted access), it can still be vulnerable to attacks. For tackling this issue, Google adds another shield to protect the user data called “Transport Layer Security”.
b. Transport Layer Security:
When data is being shared with a second person, it is called to be “in-transit”. Such data may be vulnerable to attacks from a “middle-man” that may intercept the data. Google ensures that the communication channel for data sharing is secured through HTTPS protocols. While this is enough to assure you that your data is safe in transit, it is also important to realize that security is not a permanent armor around the data file(s) being shared themselves.
In addition to this, there’s no guarantee that once the file is successfully shared, it will remain protected at the second party’s end. Google Drive acknowledges this gap and goes an extra mile to cover this concern under the “User Permissions” for each file and folder being shared.
c. Understanding User-level Permissions:
Ensuring that files remain secure even after they are shared is a partial responsibility resting with the Google Drive users. In the basic version of Google Drive, users can make sure that the data access and manipulation is limited to only those persons that are specifically granted permissions to do so. Under these settings, the users on the receiving end can either view, comment, or edit the file under discussion.
These options can allow the users to:
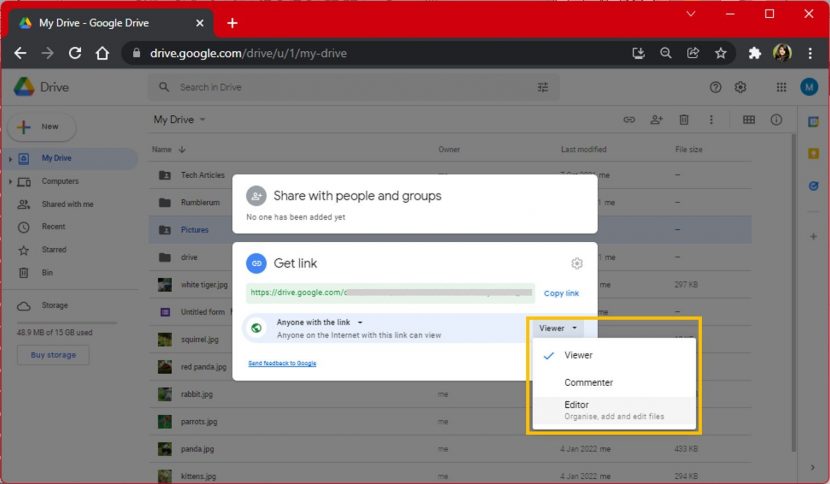
- Viewer: The link to the file is public; anyone can read the data if they get access to the link.
- Commenter: The link to the file is public; anyone can read and comment on the data if they get access to the link.
- Editor: The link to the file is public; anyone can read, comment, edit, print and download the data if they get access to the link.
There is also another option of “Restricted”. By enabling this option, only the specific users that have the link to the file can open, read, comment, and edit it.
How to Change Google Drive Permissions
Now, if you feel like you may not be doing enough on your part to keep your data secure, you can change user permissions in Google Drive by following these steps:
Step 1: Launch your browser.
Step 2: Log in to Google Drive.
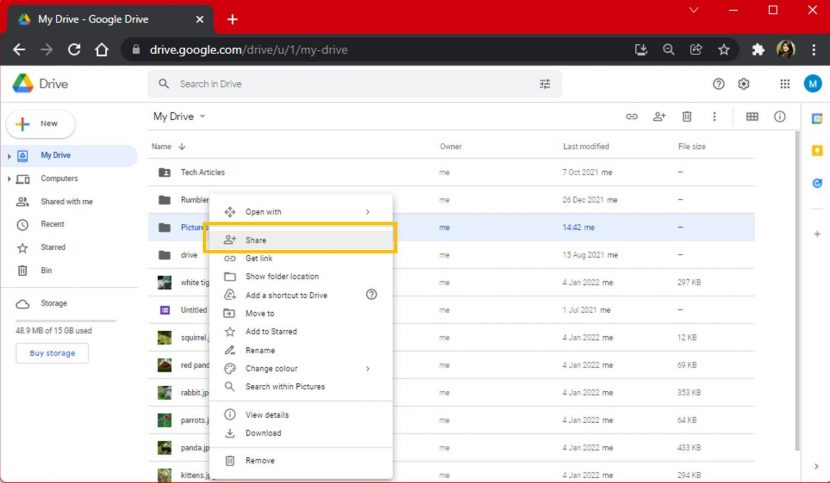
Step 3: Right-click on the file or folder that you want to share or have shared.
Step 4: From the list of options made available to you, click on “Share”.
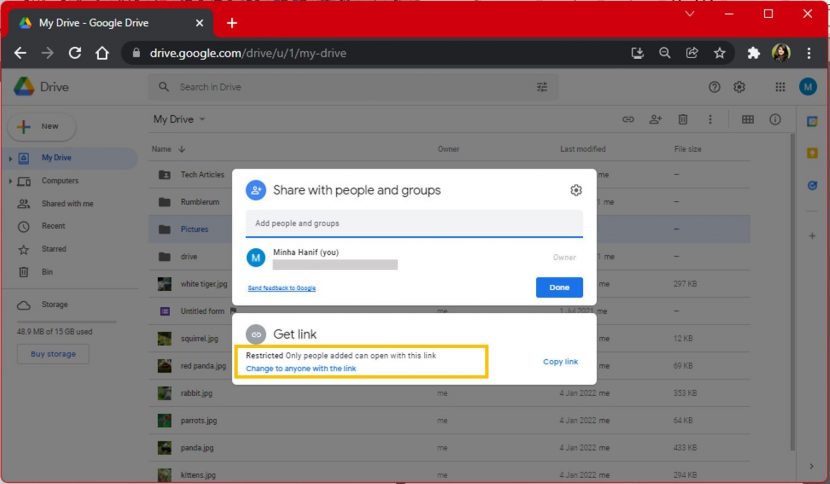
Step 5: Under the “Get Link” settings, click on “Change to anyone with the link”. If you have already granted this permission on a shared file, proceed to the next step.
Step 6: Click on the button on the right and choose from the viewer, commenter, or editor option according to the level of access you wish to give. Secondly, if you wish to roll back the permissions instead, click on “Anyone with the link” and click on “Restricted” instead.
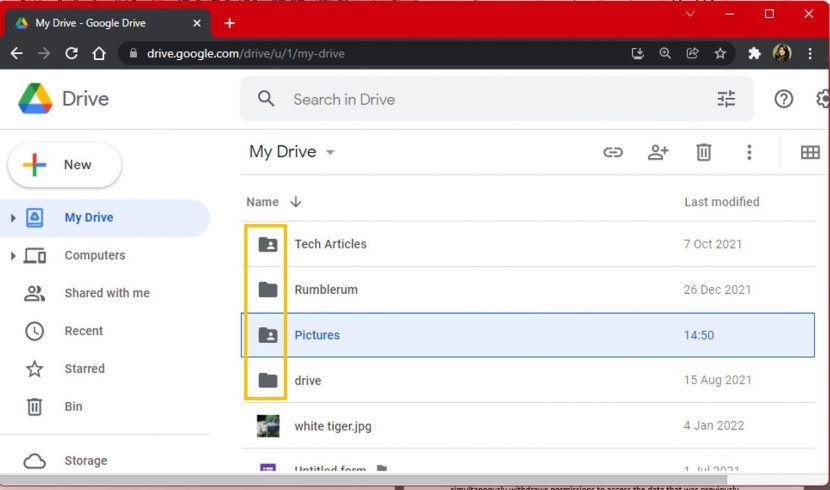
To get a broader idea of which files are shared you can spot the person-icon within the file icon. Those without this person-icon are not shared files.
In the case of files shared in Google Groups, removing a person from the group simultaneously withdraws permission from that person to access the data that was previously shared with them. In more advanced versions of Google Drive, for example, business-owned accounts, admins can restrict printing and sharing of the data as well.
Encrypting Data before Sharing on Google Drive
The encryption happens on the servers of Google. That means all the keys generated are also on the server. Google can decrypt the data at will. There is also a chance if anyone is looking for the data, they might also find the keys. Hence, it is generally advised to encrypt the data before sending the data.
If your document is supported by Microsoft Office (e.g MS Word, MS Powerpoint, MS Excel, etc.), you can use MS Office’s in-built encryption feature to encrypt the file offline and then upload it to Google Drive. This way, not even Google can read your file if it wanted to. You can encrypt PDF files on Adobe Acrobat (premium) as well.
Third-Party Encryption Services for Uploading Files to Google Drive
There are a bunch of tools available that can be used to encrypt your data. You can use applications like IBM Security Guardium Data Encryption, NordLocker, Boxcryptor, Veracrypt, Truecrypt, and 7-Zip for this purpose. This will also secure your data from Google being able to access your private documents and files.
There is, however, a small window of time when Google decrypts your data from a 256-bit key to a 128-bit key for storing. This window is very small but it does make your data vulnerable. Having already encrypted data is, hence, a good way of saving your data from such vulnerabilities.
How is Google Drive Vulnerable?
Understanding how the security system at Google works does make it seem like a reliable and economical cloud storage option. However, one might ask “But, what’s the catch?”
Well, first off, Google Drive does have the encryption keys, so you are giving them full authority to decrypt and read your files at will. The truth behind why your data may be of use to Google has much to do with surveillance capitalism. This means that Google mines your data and sells it to third-party advertisers who can give you audience-targeted content. You agree to this when you scroll down a long script and click agree to Google’s Terms of Service (ToS).
Section 11 of these Terms of Service include that:
“By submitting, posting or displaying the content you give Google a perpetual, irrevocable, worldwide, royalty-free, and non-exclusive license to reproduce, adapt, modify, translate, publish, publicly perform, publicly display and distribute any Content which you submit, post or display on or through, the Services.”
This section further reads:
“This license is for the sole purpose of enabling Google to display, distribute and promote the Services and may be revoked for certain Services as defined in the Additional Terms of those Services. You agree that this license includes a right for Google to make such Content available to other companies, organizations, or individuals with whom Google has relationships for the provision of syndicated services, and to use such Content in connection with the provision of those services.”
Lastly, since the files largely become Google’s property as well the moment you upload them to Google Drive, they might revoke your rights to access your own files. Hence, if you believe your data is sensitive (for example if you are a journalist or have the recipe to the Krabby Patty), it may be wise not to rely on Google Drive for storing or backing up your data.
Alternative Cloud Services to Google Drive
Some other cloud services that you can opt for in case you do not wish to keep using Google Drive include SpiderOak , pCloud and MEGA. These services really do not work with models that would make it easy for them to decrypt your files, making them secure. However, it is imperative that you do not forget or lose your password because your own access relies solely on it.
Making your Google Drive Account More Secure
If you wish to stick to Google Drive but want to be assured that your data is safe from hacks, you may follow these guidelines:
How secure is Google Drive? One way to enhance the security of Google Drive is to turn on two-step verification for your Google account. Protecting your Google account is the first step towards a secure Google Drive. Having a two-step verification goes a long way in securing your data on the Google platform, including Google Drive. This additional layer of security significantly contributes to the overall security of your Google Drive account. How secure is Google Drive?
You can enable 2-step verification by following these steps:
- Sign in to your Google account.
- Click on your account picture.
- Select “Manage your Google account” from the drop-down menu.
- Select “Security” from the list on the top left corner.
- Click on the 2-step verification under the “Signing in to Google tab”.
- Click on “Set it up”.
- Choose the device from which you want to do the verification. Make sure you have your Google account set up on that device and you are signed in.
Furthermore, Google recommends that you regularly run security check-ups, which you can do here. You can remove any unimportant apps connected to your account from having access. Remember to use strong, unique passwords so that your data is safe.
Bottom Line
How Secure is Google Drive ? So here it is, Google has employed over 700 security engineers that work towards keeping your data safe and secure. They remove any possible threats and deflect cybersecurity attacks. The only purpose your data is constantly under surveillance is for targeted advertisements, which is acceptable for most people who do not store sensitive data on the cloud. Hence, given that the service is not only free but also backed up by high security, Google Drive is one of the safest cloud-storage options on the internet.
We now hope you have a clear understanding of how secure is Google drive. Did you learn something from this article? Did it answer your query? We would love to hear from you. Please share your thoughts in the comments below!